
For enthusiasts and owners of legacy BlackBerry 10 devices or the BlackBerry PlayBook, the shutdown of BlackBerry’s servers in 2022 presented a major problem. After a security wipe or factory reset, it became impossible to complete the initial setup, effectively turning these classic devices into paperweights.
This tutorial will guide you through modifying the device’s firmware, allowing it to completely bypass the mandatory setup and boot directly to the home screen.
Disclaimer: This process involves modifying core operating system files. It is intended for advanced users. Proceed with caution and at your own risk. An incorrect step could potentially “brick” your device, rendering it unusable. I am not responsible for any damage to your device.
What devices have been tested?
- BlackBerry PlayBook 3G/HSPA+ running 2.1.0.1917.
- BlackBerry Z30 running 10.3.3.3216 downgraded to 10.2.1.1057 but stuck on the setup screen (bypassed by this tutorial).
Before you start
You should be familiar with using a command prompt or PowerShell terminal. This tutorial assumes you know basic commands like cd and dir.
You Will Need
- A good USB cable.
- The Autoloader file for your specific BlackBerry model.
- Sachesi: A tool for extracting files from BlackBerry Autoloaders.
- bb10mt: BlackBerry 10 MultiTool.
- A Hex Editor: I used HxD for this tutorial.
- DBBT (Darcy’s BlackBerry Tools): Used to create the final Autoloader.
- FerreiraPablo’s cap.exe: A modified Autoloader that allows you to load unsigned QCFM files.
Let’s get started.
Step 1: Split the Autoloader
First, you need to extract the core OS and Radio files from the main Autoloader executable.
- Place your device’s Autoloader
.exefile in a new folder. - Open Sachesi and navigate to the Extract tab.
- Click “Extract Signed” and select your Autoloader file.
- Sachesi will work for a few moments and then output two
.signedfiles into the same folder: one for the OS (e.g.,filename@[email protected]) and one for the Radio (e.g.,[email protected]).
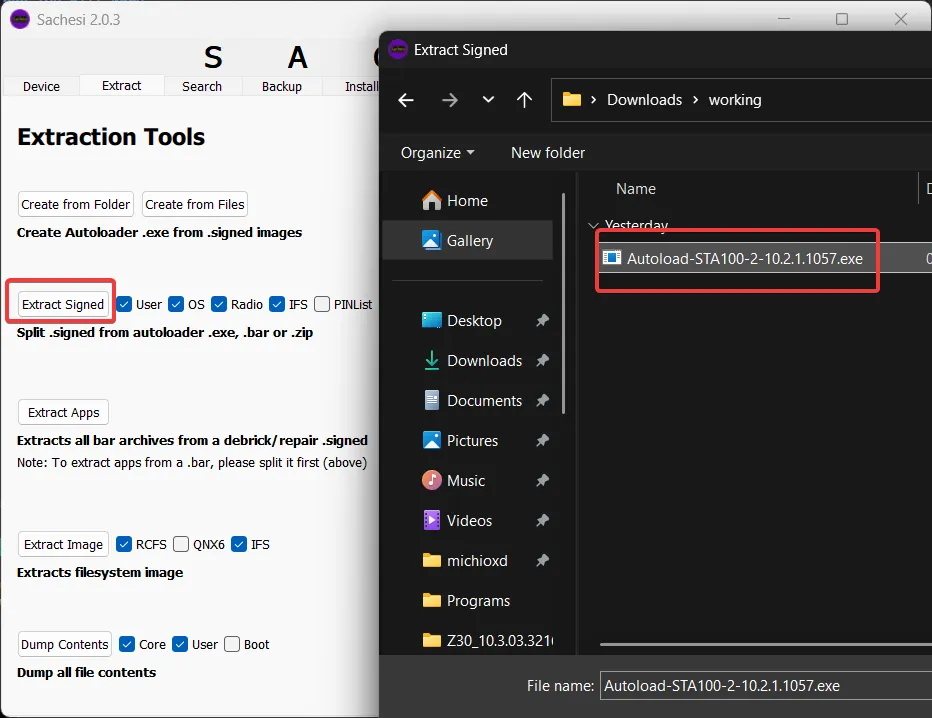
After you have extracted the files, you will have two .signed files in the same folder.
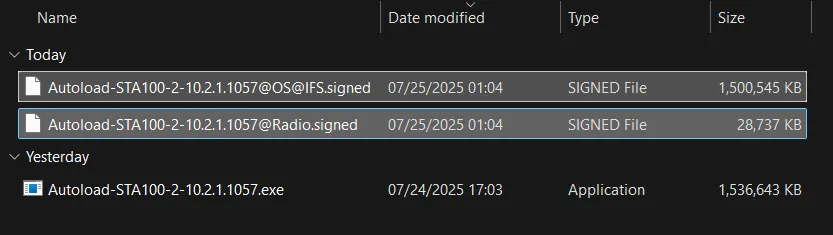
To make working with the files easier, I recommend renaming them to something more descriptive. I will rename them to OS.signed and Radio.signed.
Step 2: Unpack the Core OS File
The .signed file containing the OS is a QCFM archive. We will use the bb10mt command-line tool to unpack it.
- Open a Command Prompt or PowerShell terminal in the folder where you downloaded and extracted the
bb10mt.exefile. You can open the terminal by holding down the Shift key and right-clicking in the folder, then selecting “Open PowerShell window here”. - Run the following command. The
-cflag tells the tool the path of the file you want to unpack.
bb10mt.exe unpack -c "path\to\your\OS.signed"Replace "path\to\your\OS.signed" with the actual path to your OS file. For example:
bb10mt.exe unpack -c C:\BlackBerry\OS.signed
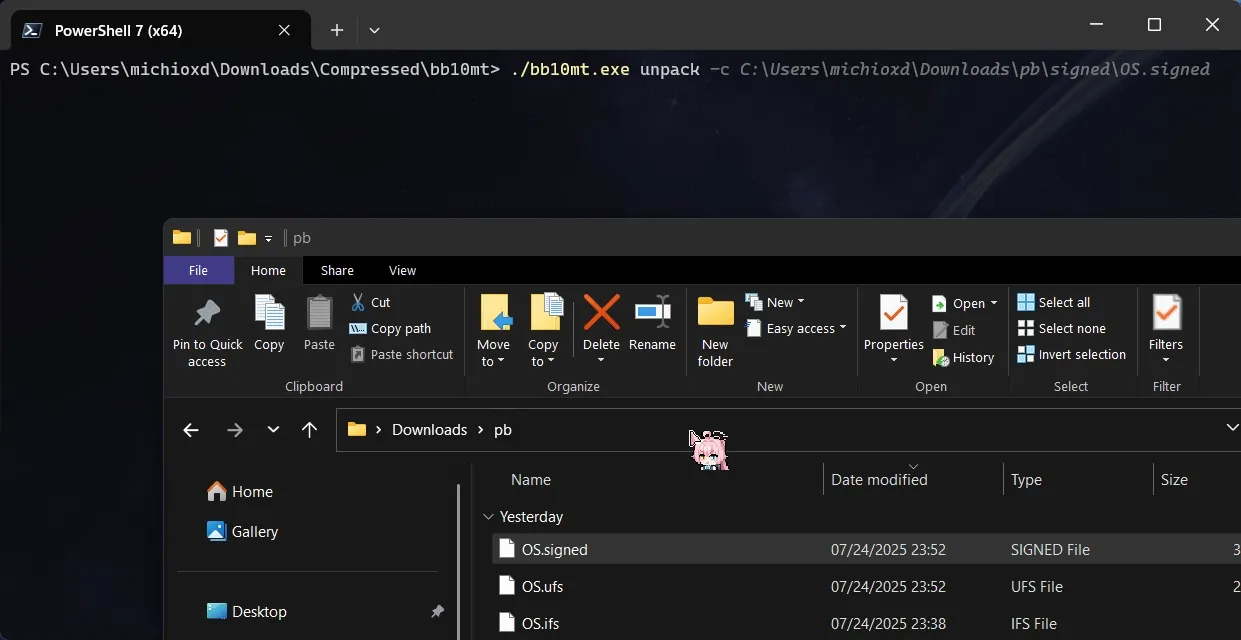
Fact: You can drop the files directly into the terminal window if you are using Windows Terminal.
After you have unpacked the files, you will have a folder with the following files:
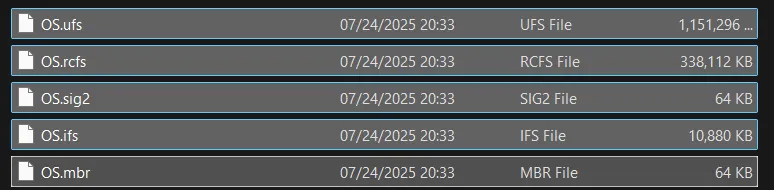
We only care about the .ufs file.
Step 3: Edit the Configuration File
This is the critical step where we disable the initial setup wizard.
Proceed carefully if you don’t want to repeat this process multiple times.
-
Open your Hex Editor (I’m using HxD).
-
Find the file with the
.ufsextension and then open it with the Hex Editor. You can drag and drop the file into the Hex Editor. -
Press Ctrl+F, then search for the text string
autorun::1.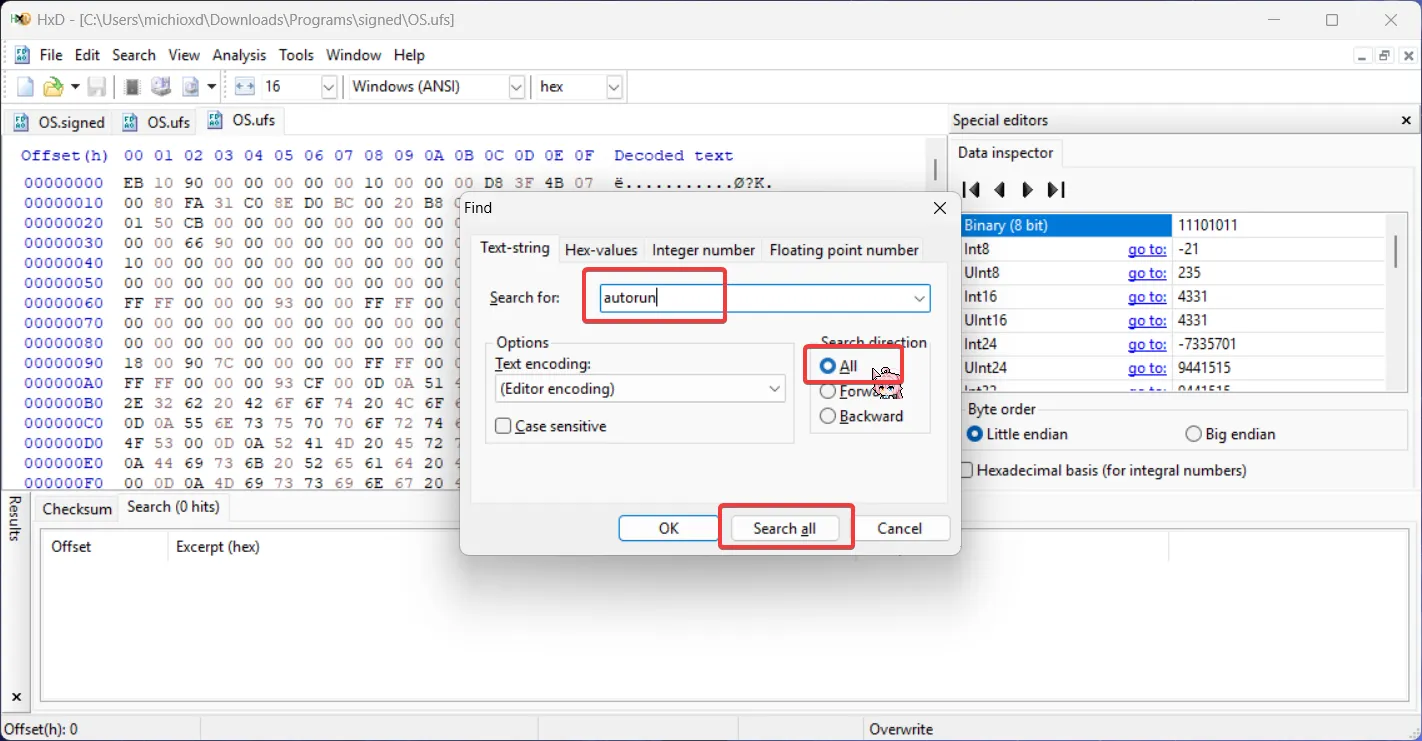
For BlackBerry 10 devices: Find the
autorun::1.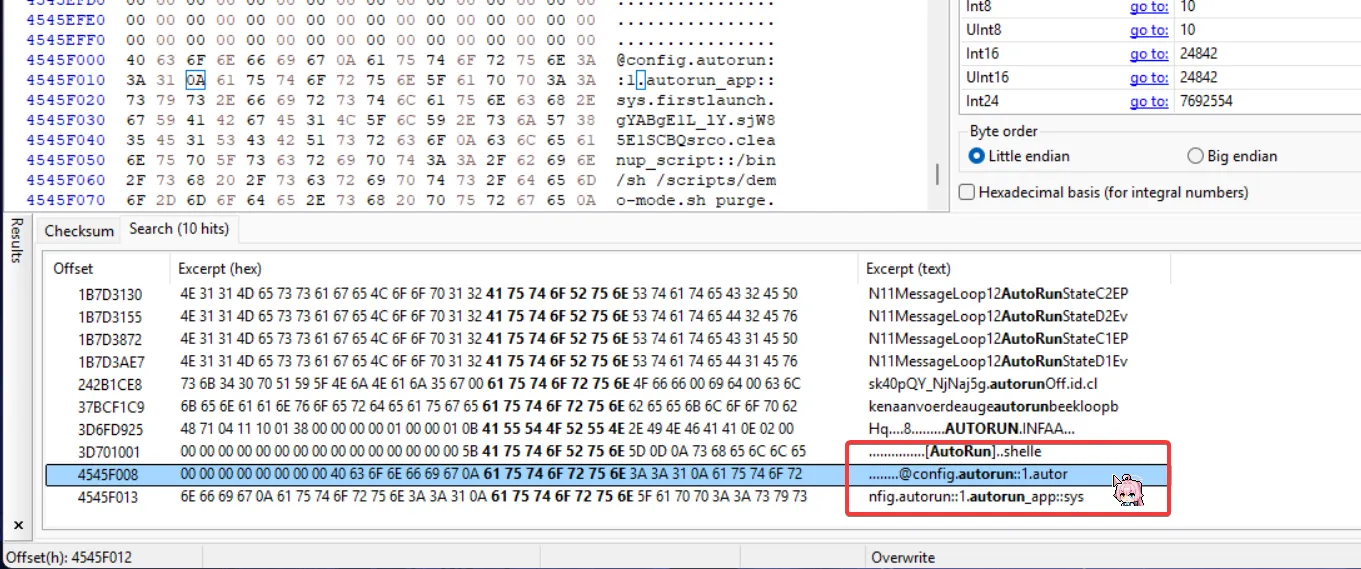
Then change it to
0: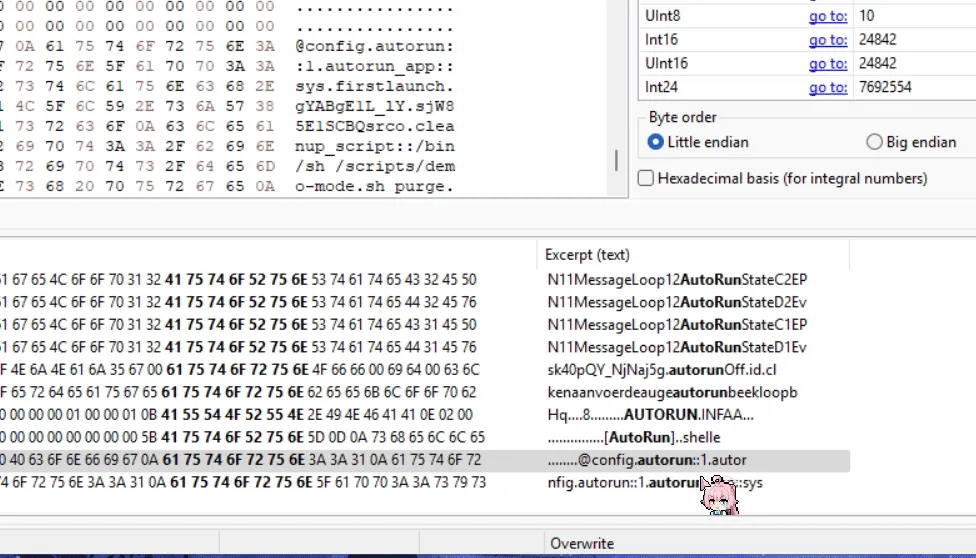
For BlackBerry PlayBook: Find the
deactivate_mode::1andautorun::1.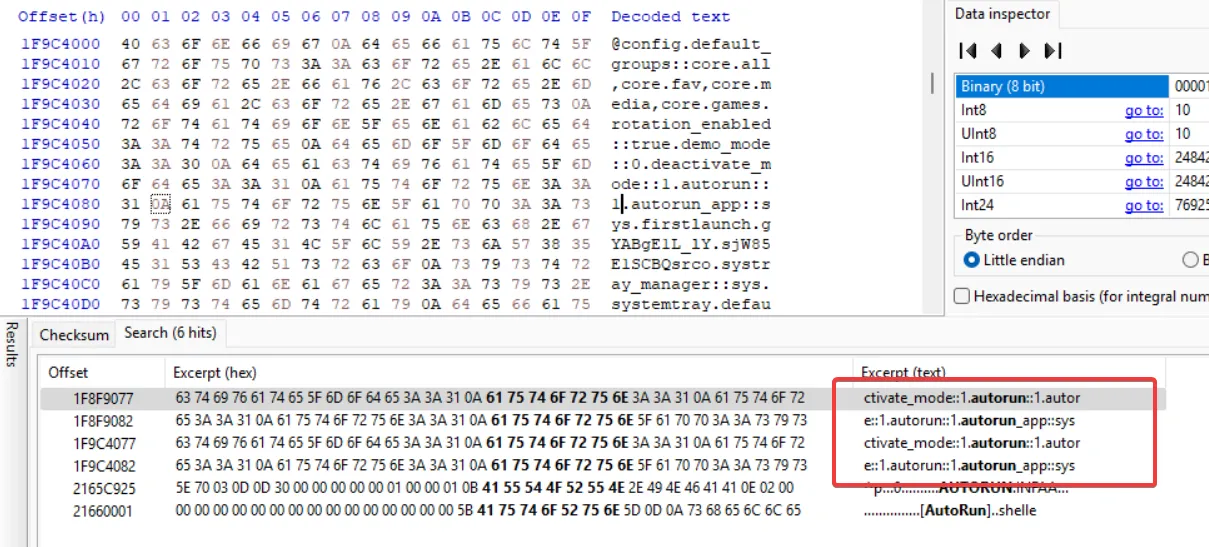
Then change it to
0, please note that there are two duplicate entries, you must change both of them: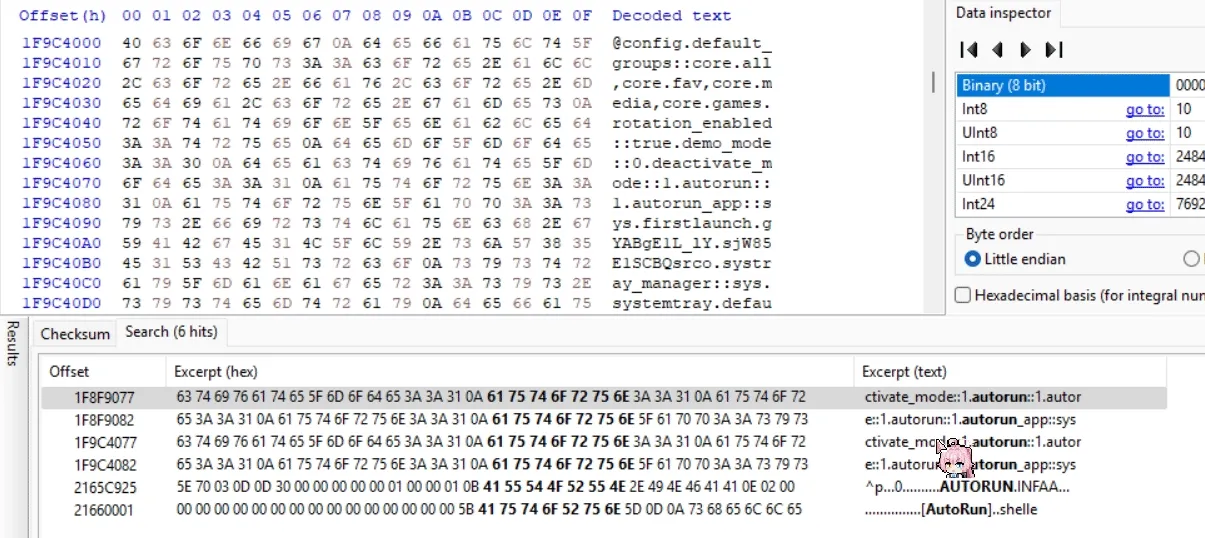
-
Save the changes to the
.ufsfile and close the Hex Editor.
Step 4: Pack the QCFM File
Now we must repack the modified files into a new .signed file.
-
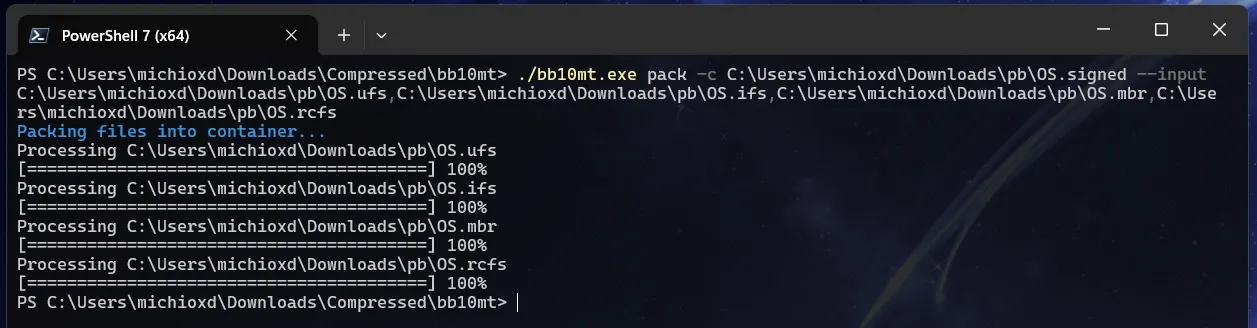
Go back to your terminal window.
-
Enter the following command structure. Be very careful with the syntax.
bb10mt.exe pack -c "path\for\output\modified_OS.signed" --input -
After typing
--input, do not press Enter yet. Go to the folder containing your unpacked files (the one with the modified.ufs). -
Select and drag the following four files onto your terminal window:
- The file ending in
.ufs - The file ending in
.ifs - The file ending in
.mbr - The file ending in
.rcfs
- The file ending in
-
The terminal will populate the paths. You must manually insert a comma (,) between each file path.
-
Important: Make sure to ignore any
.sigor.sig2files. Your final command should look something like this:bb10mt.exe pack -c C:\BlackBerry\Patched_OS.signed --input C:\BlackBerry\unpacked\OS.ufs,C:\BlackBerry\unpacked\OS.ifs,C:\BlackBerry\unpacked\OS.mbr,C:\BlackBerry\unpacked\OS.rcfs -
Press Enter.
bb10mtwill now create a new, patchedOS.signedfile at the output path you specified.
Step 5: Create the Final Autoloader
With your patched OS file ready, the final step is to build a new Autoloader .exe.
- Open DBBT (Darcy’s BlackBerry Tools). Remember to first replace its bundled
cap.exewith the modified one from FerreiraPablo. That file should be in the same folder as theDBBTool.exefile. - In the “Build Autoloader” tab, select your newly created patched OS
.signedfile and the original Radio.signedfile that Sachesi created in Step 1 (if your device requires one) by clicking … button. - Enter the name of the new Autoloader file.
- Click the “Build it!” button.
- DBBT will combine the files and create a new, fully functional Autoloader
.exein the same folder.
Flashing Your Device
You now have a custom Autoloader that will bypass the setup screen.
- Turn off your BlackBerry device.
- Run the new Autoloader
.exeyou just created. - A command window will appear then connect it to your computer via USB. As soon as you connect it, the device’s LED should turn green, indicating it is flashing.
- Once complete, your device will reboot automatically and load directly into the home screen, completely skipping the initial setup.
Congratulations! You have successfully revived your BlackBerry device. Happy hacking!